Solution Blueprints Built for Real Business Problems
Strategic, scalable, and industry-aware technology architectures designed to solve today’s challenges — and prevent tomorrow’s failures. You don’t fail because of vision. You fail because the foundation wasn’t designed to scale, adapt, or protect growth.
- Home
- / Solution Architectures
What Solution Blueprints Mean at Siffrum
At Siffrum, Solution Blueprints are not generic diagrams or pre-made templates. They are problem-first technology architectures — crafted by deeply understanding: Your industry realities Operational bottlenecks Growth expectations Security and compliance needs Each blueprint defines how systems should work together — before development begins — eliminating costly rework, delays, and instability.
Learn more
Why Businesses Need Blueprints Before Building
Most digital failures don’t happen at launch. They happen months later, when systems can’t handle growth, data, users, or change. Without the right blueprint, businesses face: Performance breakdowns Security vulnerabilities Rising maintenance costs Inflexible systems that block innovation Our Solution Blueprints are designed to remove uncertainty before execution.
How Our Blueprints Create Long-Term Value
Every Solution Blueprint at Siffrum is: Industry-aware, not generic Scalable by design, not patched later Security-aligned, not added as an afterthought Future-ready, not limited by current requirements This ensures faster execution today — and stability tomorrow.
.drawio.png)
Scalable Cloud Web Architecture
Designed for high availability using load balancers, auto-scaling, and managed databases.
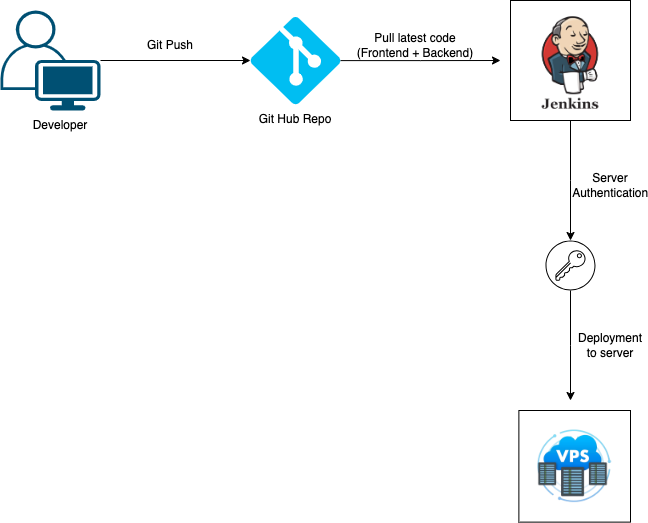
CI/CD Pipeline Architecture
Automated build, test, and deployment pipeline ensuring faster releases and zero downtime.
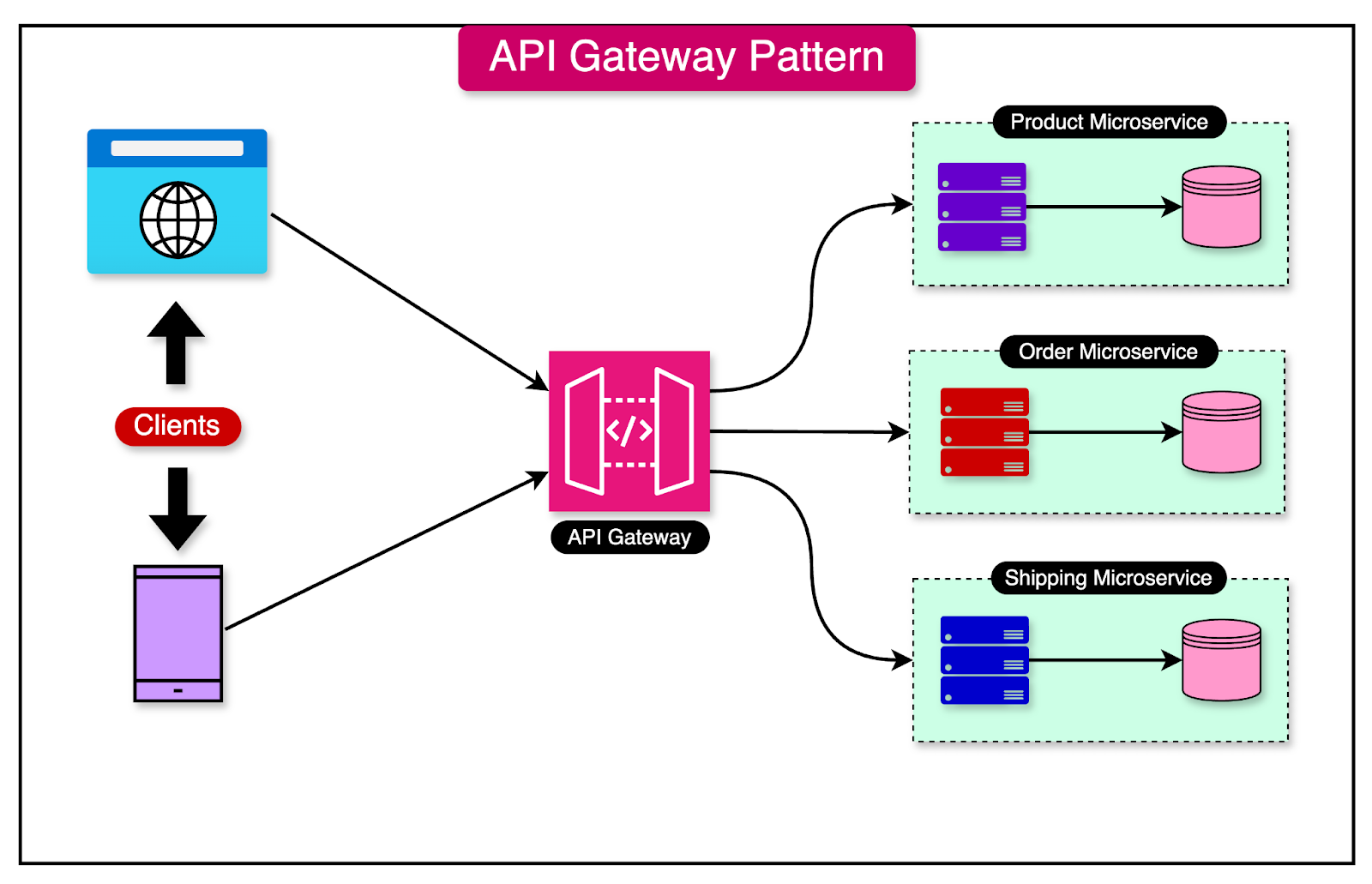
Microservices Architecture
Decoupled services with API gateway, service discovery, and centralized observability.
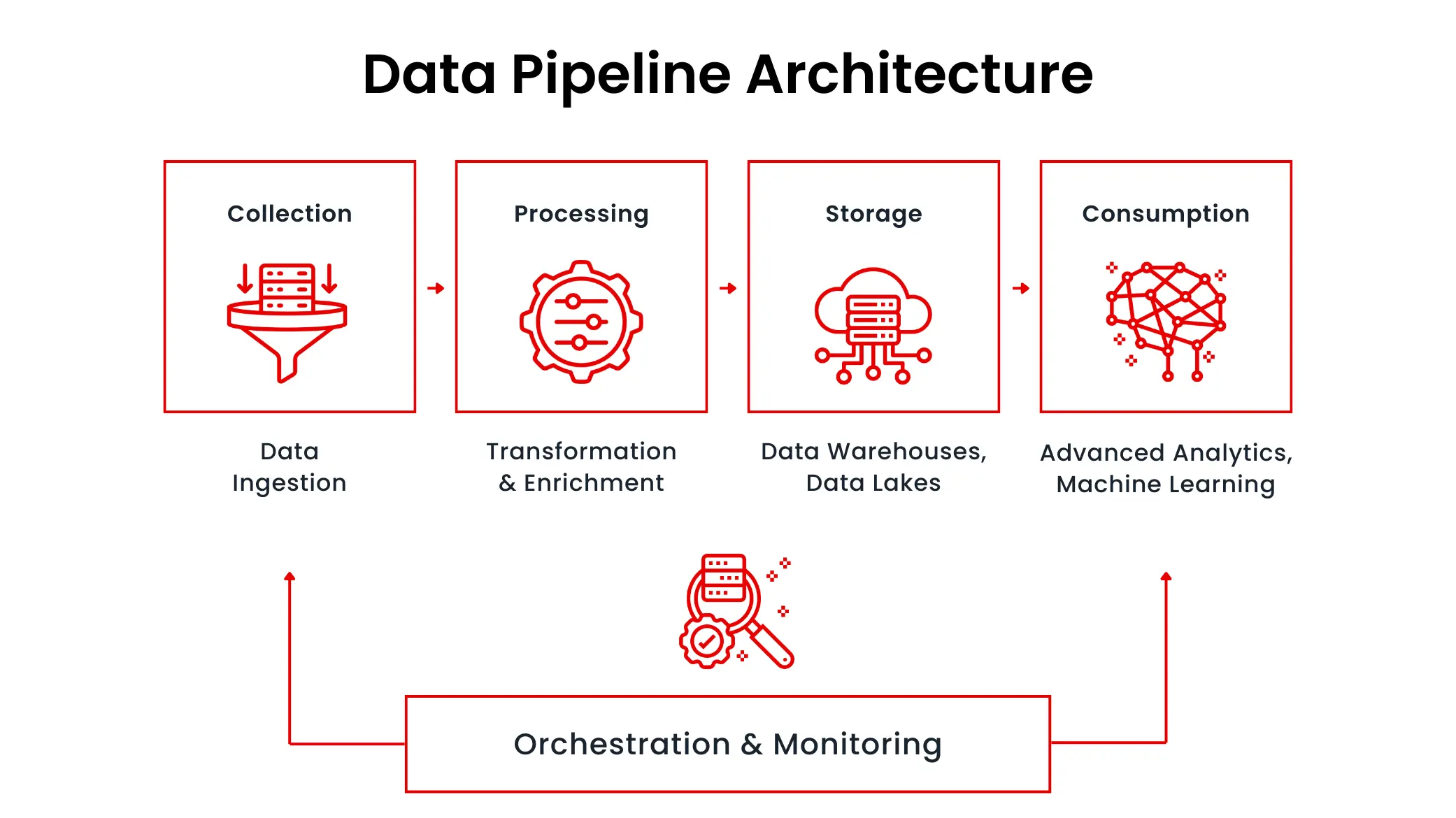
Data & Analytics Architecture
Centralized data pipelines for ingestion, processing, analytics, and business intelligence.
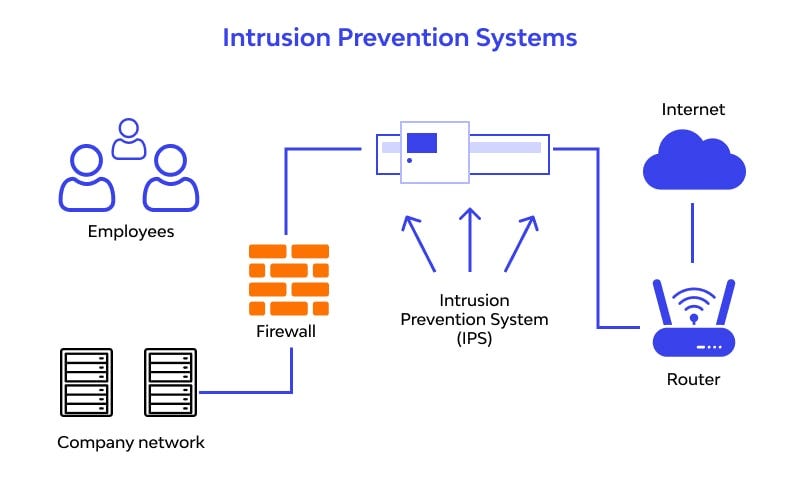
Secure Enterprise Architecture
Defense-in-depth security model with IAM, encryption, logging, and compliance controls.
